BBS Telnet Access is Temporarily Closed due to Brute Force Penetration Attempts. 09/21/16 see resolution update posted below.
Someone has been brute force attacking the BBS via port 23 – Telnet. Unfortunately for the time being we were forced to close Wildcat’s telnet port shutting off anyone trying to connect to the bbs via this method.
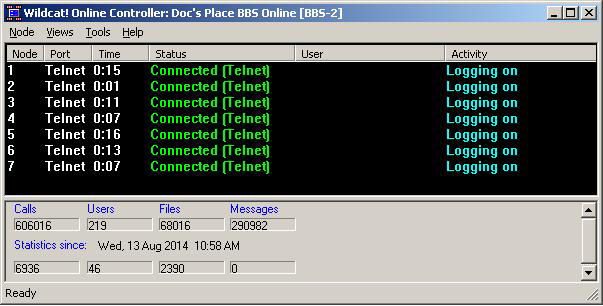
Wildcat 5 BBS software was way advanced in its day and is highly configurable. The ability to change ports on the web http side was also an advance feature, but unfortunately the only Telnet option is to turn it on or off, but not change the access port.

We only have a couple of Telnet users accessing the bbs. Unfortunately due to security concerns for our network Telnet access must be closed. We are working on a solution. Possibly running the bbs under our existing CloudFlare account.
Update 09/21/16: It is being reported that certain SOHO Routers have an inherit vulnerability that can allow an attacker network access on port 23. This is what so called “script kiddies” are remotely scanning for. It’s a form of War Driving, similar to modem dialing a series of phone numbers looking for modems that answered (Movie War Games) but scanning a block of IP’s instead.
We have reached a solution that is allowing BBS Telnet access again, but are not announcing it in this post for security reasons. Users accessing the BBS by Telnet have been notified of the new login routine. 😉
